Узнайте о признаках предательства и как их распознать. Гадание на измену по одной карте поможет вам оценить ситуацию и принять правильное решение в вашем отношении.
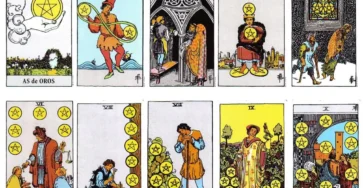
Исследование современных тенденций онлайн таро: как меняется популярность и восприятие этой практики.
Онлайн таро, несомненно, стало неотъемлемой частью современной духовной практики. В последние годы мы наблюдаем рост интереса к этой традиционной форме…

Как работает гадание на любимого человека?
Гадание на любимого онлайн бесплатно основано на энергии и символизме карт. Это позволяет вам лучше понять вашего партнера, разгадать его мысли и понять его чувства.

«Таро и художественное творчество: вдохновение и творческий процесс через карты»
Вступление Искусство Таро не только помогает предсказывать будущее, но и становится источником вдохновения для художников и творцов. Узнайте, как карты…

Что думает обо мне мужчина: расшифровка тайн с помощью гаданий
что думает обо мне мужчина гадание на картах таро — полный раскалад на картах.

Таро и Личное Самопонимание: Разгадайте, Что Со Мной Не Так
Отправьтесь в увлекательное путешествие в свой внутренний мир с помощью карт Таро, чтобы раскрыть ответы на вопросы о себе. Узнайте,…

Таро и Восприятие: Разгадайте, Как Вас Видят Люди
Откройте для себя, как карты Таро могут стать зеркалом, отражающим восприятие других о вас. Узнайте, как гадание на Таро может…

Таро и Путешествия: Как Определить Успешность Вашей Поездки
Отправляетесь в путешествие и хотите узнать, какое вас ожидает приключение? Узнайте, какие карты Таро могут предсказать успешность вашей поездки и…

Тайны Магии Таро: Почему Пророчества Сбываются
Узнайте, почему карты Таро считаются мощным инструментом предсказаний и как их магия способствует сбыванию пророчеств. Разгадаем тайны влияния Таро на…

Таро и Отношения: Предвидение Будущего с Мужчиной
Откройте для себя, как карты Таро могут стать вашим проводником в мире отношений с мужчиной. Раскройте тайны будущего, используя уникальные…
